| |
|
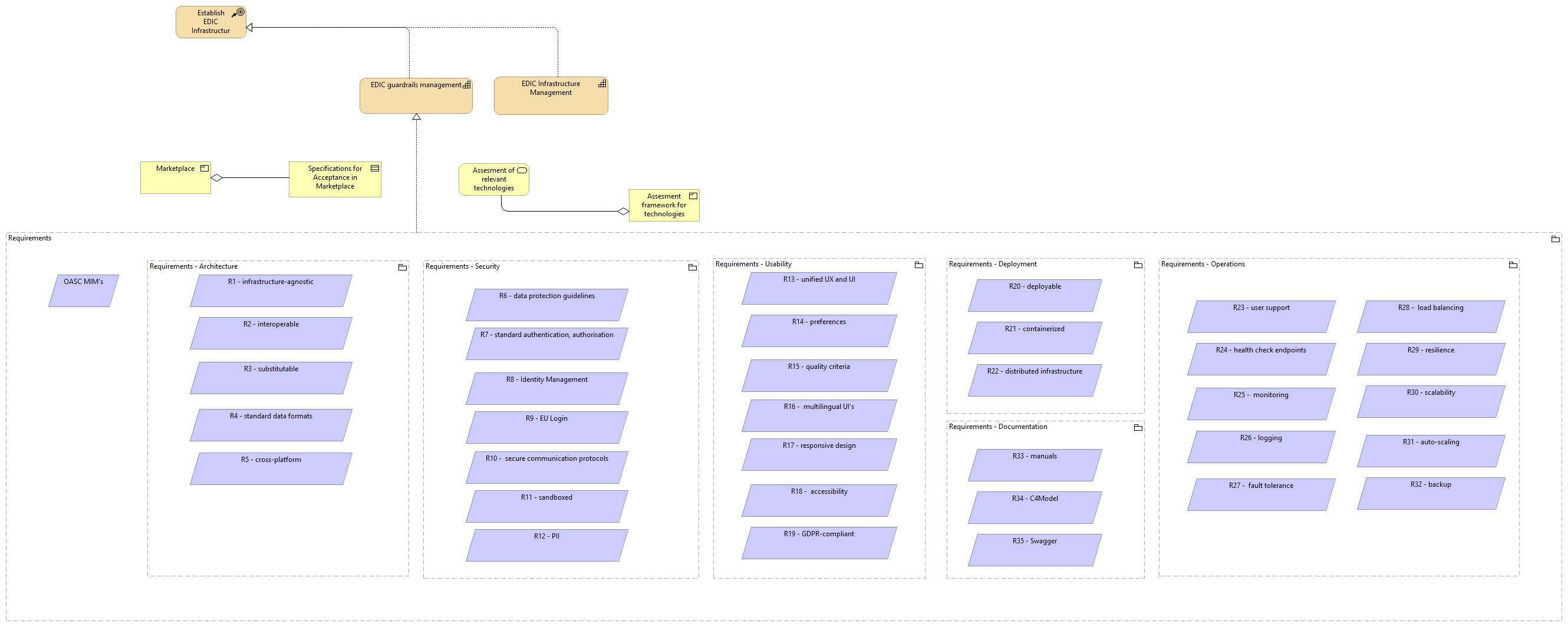
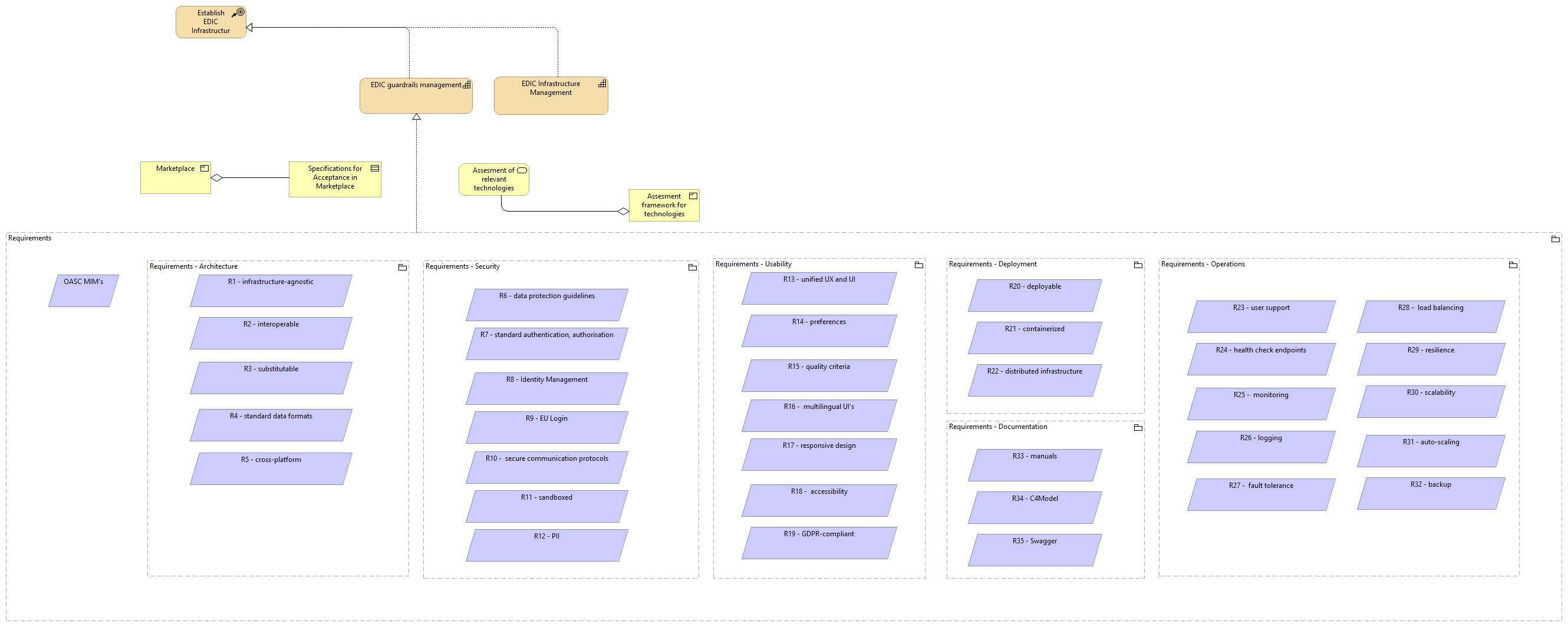
Requirements |
Requirements - Documentation |
| |
|
Requirements |
Requirements - Usability |
| |
|
Requirements |
Requirements - Operations |
| |
|
Requirements |
Requirements - Architecture |
| |
|
Requirements |
Requirements - Deployment |
| |
|
Requirements |
OASC MIM's |
| |
|
Requirements |
Requirements - Security |
| |
|
Requirements |
EDIC guardrails management |
| |
|
Requirements - Documentation |
R35 - Swagger |
| |
|
Requirements - Documentation |
R34 - C4Model |
| |
|
Requirements - Documentation |
R33 - manuals |
| |
|
Requirements - Usability |
R13 - unified UX and UI |
| |
|
Requirements - Usability |
R14 - preferences |
| |
|
Requirements - Usability |
R19 - GDPR-compliant |
| |
|
Requirements - Usability |
R17 - responsive design |
| |
|
Requirements - Usability |
R18 - accessibility |
| |
|
Requirements - Usability |
R15 - quality criteria |
| |
|
Requirements - Usability |
R16 - multilingual UI's |
| |
|
Requirements - Operations |
R28 - load balancing |
| |
|
Requirements - Operations |
R31 - auto-scaling |
| |
|
Requirements - Operations |
R25 - monitoring |
| |
|
Requirements - Operations |
R27 - fault tolerance |
| |
|
Requirements - Operations |
R29 - resilience |
| |
|
Requirements - Operations |
R30 - scalability |
| |
|
Requirements - Operations |
R32 - backup |
| |
|
Requirements - Operations |
R23 - user support |
| |
|
Requirements - Operations |
R24 - health check endpoints |
| |
|
Requirements - Operations |
R26 - logging |
| |
|
Requirements - Architecture |
R3 - substitutable |
| |
|
Requirements - Architecture |
R5 - cross-platform |
| |
|
Requirements - Architecture |
R1 - infrastructure-agnostic |
| |
|
Requirements - Architecture |
R4 - standard data formats |
| |
|
Requirements - Architecture |
R2 - interoperable |
| |
|
Requirements - Deployment |
R22 - distributed infrastructure |
| |
|
Requirements - Deployment |
R21 - containerized |
| |
|
Requirements - Deployment |
R20 - deployable |
| |
|
Requirements - Security |
R6 - data protection guidelines |
| |
|
Requirements - Security |
R10 - secure communication protocols |
| |
|
Requirements - Security |
R11 - sandboxed |
| |
|
Requirements - Security |
R12 - PII |
| |
|
Requirements - Security |
R7 - standard authentication, authorisation |
| |
|
Requirements - Security |
R8 - Identity Management |
| |
|
Requirements - Security |
R9 - EU Login |
| |
|
Marketplace |
Specifications for Acceptance in Marketplace |
| |
|
EDIC Infrastructure Management |
Establish EDIC Infrastructure |
| |
|
EDIC guardrails management |
Establish EDIC Infrastructure |
| |
|
Assesment framework for technologies |
Assesment of relevant technologies |